How to prevent DDoS in Apache ?
Prevent DDoS
in Apache & IP Block Automation
DDoS (Distributed Denial of Service) attacks are a type of cyberattack that can cause serious damage to your web server. These attacks involve flooding your server with a huge volume of traffic, overwhelming its resources and causing it to crash. In this blog post, we'll discuss how to prevent DDoS attacks in Apache, without using any third part tool/application.
Available
Options to Prevent DDoS :
You can use various mentioned methods to achieve the same. But using WAF, CDN, etc will cost extra dollars. Which might not be necessary for a small scale application.
- Use a Web Application Firewall (WAF): A WAF can help detect and block malicious traffic before it reaches your Apache server. It can also help block common attack vectors, such as SQL injection and cross-site scripting (XSS).
- Install mod_evasive: mod_evasive is an Apache module that helps detect and block DDoS attacks. It works by tracking the number of requests from each IP address and blocking requests that exceed a certain threshold.
- Use rate limiting: Rate limiting can be used to restrict the number of requests that can be made to your Apache server from a single IP address. This can help prevent DDoS attacks by limiting the amount of traffic that can be sent from a single source.
- Configure your server properly: Make sure your Apache server is configured properly and all unnecessary modules are disabled. Also, make sure you have the latest security patches and updates installed.
- Use a CDN: A Content Delivery Network (CDN) can help distribute your content across multiple servers and data centers, which can help absorb DDoS attacks and reduce their impact on your Apache server.
- Monitor your server: Regularly monitor your Apache server for unusual traffic patterns and unexpected spikes in traffic. This can help you detect and respond to DDoS attacks in a timely manner.
In this blog we will discuss the default Apache service mod_evasive which can help to prevent DDoS for Apache & also block the attacker IP.
Mod_evasive is an Apache module that can help prevent DDoS (Distributed Denial of Service) attacks by tracking the number of requests from each IP address and blocking requests that exceed a certain threshold.
we'll discuss how to use mod_evasive in Apache to protect your web server from DDoS attacks.
- Installation of mod_evasive :
To use mod_evasive, you first need to install the module on your Apache server. The installation process will vary depending on your operating system and package manager.
On Ubuntu or Debian, you can install mod_evasive using the following command:
Ubuntu / Debian : sudo apt-get install libapache2-mod-evasive
RHEL / CENT OS : sudo yum install epel-release
- Configure mod_evasive :
After installing mod_evasive, you need to configure the module to suit your specific needs. The configuration file for mod_evasive is located at /etc/apache2/mods-available/mod-evasive.conf on Ubuntu and Debian systems. You can use a text editor such as nano or vim to edit the file.
Here are some of the most important configuration options for mod_evasive:
- DOSHashTableSize: This option sets the size of the hash table used to store IP addresses and request URLs. The default value is 3097, but you may want to increase it if you have a high-traffic website.
- DOSPageCount: This option sets the number of requests allowed for the same page within the DOSPageInterval time period. The default value is 2, but you can adjust it based on your needs.
- DOSSiteCount: This option sets the number of requests allowed for the same site (based on the server name) within the DOSSiteInterval time period. The default value is 50.
- DOSPageInterval: This option sets the time period (in seconds) for counting requests for the same page. The default value is 1.
- DOSSiteInterval: This option sets the time period (in seconds) for counting requests for the same site. The default value is 1.
- DOSBlockingPeriod: This option sets the amount of time (in seconds) that an IP address will be blocked if it exceeds the request thresholds. The default value is 10.
Example configuration :
<IfModule mod_evasive24.c>
# Basic settings
DOSHashTableSize 3097
DOSPageCount 2
DOSSiteCount 50
DOSPageInterval 1
DOSSiteInterval 1
DOSBlockingPeriod 10
# Email notifications ( Optional , only if you need e-mail notification)
DOSEmailNotify admin@example.com
DOSSystemCommand "sudo /usr/bin/perl /usr/local/bin/mod_evasive.pl"
DOSLogDir "/var/log/mod_evasive"
# Whitelisting ( request will not be counted from these IP's)
DOSWhitelist 127.0.0.1
</IfModule>
You can also configure mod_evasive to send email notifications when an IP address is blocked, whitelist certain IP addresses, and set custom error messages.
- Enable mod_evasive
After configuring mod_evasive, you need to enable the module in Apache by creating a symbolic link to the configuration file in the mods-enabled directory. On Ubuntu and Debian systems, you can use the following commands:
sudo a2enmod evasive
sudo systemctl restart apache2
- Monitor mod_evasive
After enabling mod_evasive, you should monitor the module to make sure it's working correctly. You can check the mod_evasive logs for blocked IP addresses and adjust the configuration if necessary. You can also use tools such as Apache Bench or Siege to simulate DDoS attacks and test mod_evasive's performance.
The module sends a 403 error to the hacker. By default, this also include a 10 second waiting period o the blacklist. If the IP address making the request tries again in the 10 second window, the waiting time increases.
In conclusion, mod_evasive is a powerful tool that can help protect your Apache web server from DDoS attacks. By configuring mod_evasive to suit your specific needs and monitoring the module regularly, you can ensure that your website stays up and running even in the face of a DDoS attack.
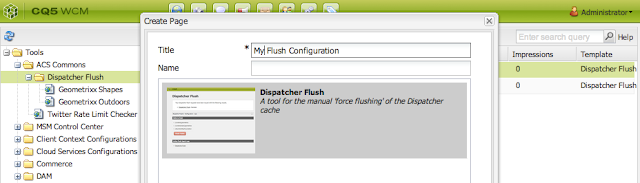
For Prevention of DDoS in AEM you also refer Article
How to prevent DOS attacks in AEM ?









Comments
Post a Comment